A fresh pre-election scandal has erupted in the US. Unknown hackers, allegedly Russian, attempted to hack the email of a presidential front-runner, Hillary Clinton. American cyber-security boffins claim there were at least five separate attack attempts. Virus-laden mails arrived from fake addresses, doctored to look like speeding-fine e-tickets. However, it remains unclear if any data was harvested, whether these attempts really stem from Russia, or if such hacks might succeed.
American Protection
The initial impression is that cyber-protection in the US, a high-tech heavyweight, is in good shape. The strategy for military cyber-ops is thought-out and set-up with infrastructure protection installed, collaboration with allies secured, and the aim of staying several steps ahead of the enemy on cyber-technology. In 2011, the White House announced that cyber attacks on the USA or its allies would be classed as hostilities, with payback of the most serious kind, including economic sanctions and military assault.
All operations to safeguard America on the digital front lines are led by the United States Cyber Command, a unit set up in 2009. It is commanded by Admiral Michael S Rogers, a seasoned campaigner in the battle of the bytes, who led the cyber attacks on Iraq during the American invasion of 2003. Under his command is a whole cyber-force of every conceivable kind, the Second Army, the Tenth Fleet, the 24th Air Force, and the Cyber-Command of the Marine Corps. Soldiers on the digital front can be promoted to many ranks, including cyber-officer, cyber-technician, or cyber-specialist.
The Great Firewall of China
There is no mention in any American strategic documents of who exactly is such a threat to the US. However, the de facto villain of the piece was unmasked long ago, the People's Republic of China. Although China lags behind the US in the size of its naval and air fleets, it initially held the lead in the digital sector. The Chinese began developing their cyber-warfare strategies as early as 1995, and launched their own cyber-command, the Network Forces, nine years earlier than the Americans.

How the cyber-conflict began between America and China isn't known. Most probably it began with small provocations, which escalated into full-scale conflict. The US believes that 2010 was the watershed in cyber-hostilities – when unknown hackers attacked 35 of the USA's largest corporations, including Google, Northrop Grumman, Symantec, Yahoo, Dow Chemical, Adobe Systems and others – stealing valuable scientific and military information.
China steadfastly denies these claims, blaming them dually on sinophobia and American attempts to sweep its own misdeeds under the cyber-carpet. Washington likewise avowed that it has undertaken no kind of hostile actions towards China. In the midst of this standoff Edward Snowden appeared, claiming that American cyber-warriors have been intercepting Chinese SMS traffic for years, and have penetrated the networks of the foremost scientific research centers in China.
CIA pulls staff from Beijing following a cyber attack on government employees http://t.co/xHrSDNUZrg pic.twitter.com/4Lm748UkdM
— The Telegraph (@Telegraph) October 3, 2015
The US underestimated the Chinese threat for a long while. Even as recently as 2012 it was thought that China was only capable of mounting primitive denial-of-service internet attacks, which can be swatted quite simply. This haughty American scorn for their opponents cost them dearly in August 2015, when Chinese hackers broke into the Personnel Office of the US Administration network, which holds the personal data of everyone who has ever worked for the US government in any capacity. How much data was hacked remains unknown. John McAfee, the security systems developer and one of the world's most famous names in the field of cyber security believes the personal data of up to 14 million people, who have worked for the US government over the past 25 years, was compromised. McAfee claims that this data has fallen into Chinese hands, and that it includes the details of American agents who exercise influence over foreign governments.
“America is under attack. An invasion is under way in America,” McAfee plaintively declared. “There are Chinese digital boots trampling the good earth of our nation. Our government is consumed by insanity and paranoia — they are corrupt and useless.”
China arrested Hackers at US Govt. Request. Would US do Same on China's request? http://t.co/6RFpjJUou2 #Security pic.twitter.com/Qz5Gtp8mvR
— The Hacker News (@TheHackersNews) October 10, 2015
It's hard to say how much truth lies among McAfee's rhetoric, but the damage was clearly significant – since the US immediately began threatening to impose economic sanctions on China. The Chinese litany runs that the theft was undertaken by lone hackers. Despite this, in 2013 the Mandiant corporation issued a report confirming that cyber attacks on US military targets could be traced to a Chinese military unit numbered № 61398, and based in a twelve-story building in Shanghai.
The standoff was defused during the official visit of Chinese Premier Xi Jinping to the United States. A memorandum on cessation of digital espionage was signed, alongside coordinated efforts to prevent cyber crime. The memorandum provoked skeptical stares among American security experts. Few of them believe that Beijing will really stop its operations against the US, especially since these have netted them lucrative new technologies and helped China to operate effectively in the international arena.
Patriotic Hackers in the Kremlin's service
The US's second-most dangerous foe is Russia. This is not least because while Chinese hackers may often wear uniforms, their counterparts in Russia come with their own ideas, and work on their own initiative. Despite many efforts, neither American nor European cyber-security experts have been able to amass any tangible evidence that the Kremlin is behind the Russian hackers.
On top of that, analysis of the powerful cyber-attacks on Georgia during the 2008 war shows computer activity not based merely in Russia — but throughout practically the entire post-soviet diaspora, including the Baltic States. It's also been asserted that these attacks were committed by private individuals who supported Moscow's policy during the hostilities, and who worked on an entirely voluntary basis.
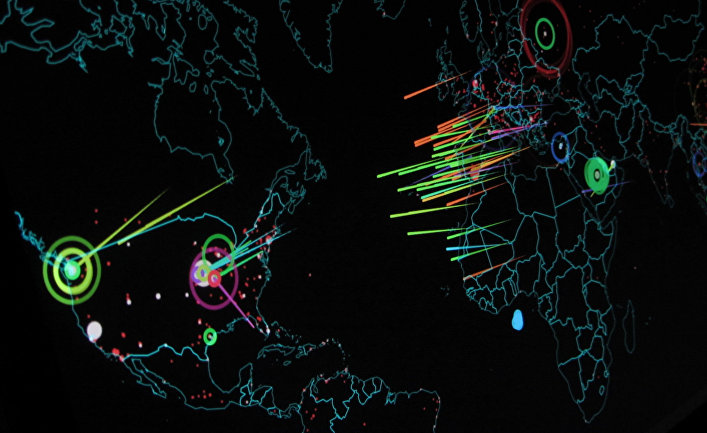
Visualized in real-time, all the world's cyberattacks looks like global thermonuclear war: http://t.co/Cb80z5SOHu pic.twitter.com/JraYvTrMiW
— Co.Design (@FastCoDesign) October 8, 2015
No evidence could be found. In February 2014 the western media went public about a web-virus code-named “Snake”, found in Ukrainian networks, while in October the same year, iSight claimed that Russian hackers had long been exploiting a bug in the Windows OS to harvest information from NATO and EU computers. Obviously there are sections within the Russian Ministry of Defense and the Russian Secret Service involved with cyber-security. With this in mind, in March this year came an announcement that a Russian state bureau dealing with the detection, prevention and elimination of cyber-attacks had been formed. The Federal Security Bureau's (FSB) National Coordination Centre for Computer Incidents was nominated as the hub of the new bureau. The Defense Ministry's cyber-section first appeared officially two years ago — and in 2015 it announced a concept development plan for information technology for the next five years.
Stories about the work of pro-government Russian hacker groups make up the stock-in-trade of the Western press. Security experts in the USA, EU, and at NATO claim these have amounted to large-scale economic and political espionage over recent years. Western experts suggest that these activities stem from a single organizational planning centre. Moreover, it is claimed, Russian hackers strive diligently and steadfastly, as opposed to the more haphazard work of their long-suffering Chinese counterparts.
Despite all the claims, evidence that such groups exist, under Kremlin patronage, hasn't surfaced, nor is it likely to. Quite the opposite – Moscow has continuously showed its readiness for collaboration. This was how the first-ever US-Russian Cyber Non-Aggression Pact was concluded, in the presence of Barack Obama and Vladimir Putin in 2013, with a hot-line set up to prevent the escalation of cyber-incidents.
The Islamic Cybernetic Republic
If aggressors are hard to identify in cyberwars with the US, Russia, or China, then everything is crystal clear in the case of Iran. In 2006 American hackers, in collaboration with their Israeli colleagues, developed a computer virus which put a malevolent cyber-spoke in the wheels of Iran's uranium enrichment plant at Natanz. By 2010, one in five of the centrifuges was out of action, and experts estimate that the Iranian nuclear program was put back by approximately two years. The virus got into the network due to staff neglect, and was nicknamed Stuxnet once discovered. The entire operation was informally titled 'The Olympic Games.”The USA never officially acknowledged its involvement in the stunt.
Tehran didn't dither when retaliating. The Iranian Cyber Command appeared in November 2010, as a wing of the Iranian armed forces. The development delivered instant pay-offs, a wave of further viruses was quickly found, whose code suggested that the creators were very familiar with Stuxnet. Iran didn't dally, and over the following years the US suffered a barrage of cyber-attacks, of which Operation Newscaster was the most infamous case. Iranian hackers set up fake IDs on social networks, supposedly accounts held by independent western journalists, even supported by their names and alleged biographies. An entire bogus web news service appeared at NewsOnAir.org, with content created by independent journalists from western nations, with re-hashed material culled from wire agencies. The ruse garnered the credulity of American, British, Israeli and Saudi officials, analysts and military advisors – who soon fell into chummy correspondence, during which infected files hacked into their passwords to proffer access to secret information.
The risk of a serious cyber attack on civil nuclear infrastructure is increasing. http://t.co/Y7973tW6mR pic.twitter.com/R6NDnOpRZ0
— Internat'l Security (@ChathamHouseISR) October 5, 2015
Working hand-in-hand with the Iranian military is a group of volunteer hackers from the Islamic Revolutionary Guard Corps, united in the Iranian Electronic Army. They've chalked up many a victory in social networks, and are believed to have been behind hacking the IAEA website in 2012.
Digital warfare grows more widespread with each passing year. It's hardly surprising that countries who find the costs of conventional armies too pricey plunge headlong instead into digital warfare. Major world powers have long gone head-to-head in invisible confrontations in which the stakes range from millions of dollars of technology through to the good reputation of promising policies. These wars are waged anonymously, deciding who has been hit might be possible in theory, but remains almost impossible to prove. Even so, just one single experienced hacker can deal a severe blow to the opponent's defenses, not to mention what an organized group of cyber-troops could achieve in paralyzing a whole country's nuclear program, or smearing a presidential hopeful.